It’s no secret that malware is getting increasingly more sophisticated. The most recent example was identified by Microsoft and carries the name Zemot. A recent report by Malwarebytes suggests that the cyber criminals behind Zemot are using a number of popular websites to spread their malware, including Last.fm and The Times of Israel. The malware was distributed via Google’s DoubleClick service, along with Zedo advertising agency – both of which have a very broad reach.
“It was active but not too visible for a number of weeks until we started seeing popular sites getting flagged in our honeypots,” wrote Jerome Segura, a senior security researcher at Malwarebytes. “That’s when we thought, something is going on.”
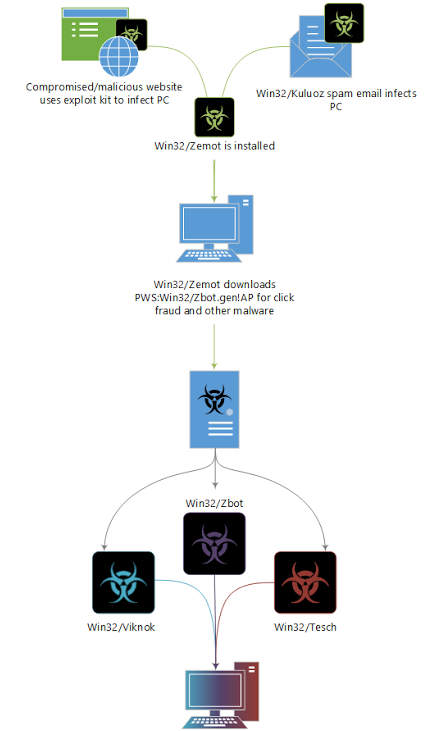
The malicious ads work by using the Nuclear exploit, which looks for an unpatched version of the Internet Explorer or an Adobe Flash Player running on the victim’s computer. The ads then download the Zemot malware, which in turn downloads a variety of additional malicious applications. The malware mainly targets Windows XP users (although not exclusively), and computers with an outdated antivirus software.
A plan of attack for the malicious ads;
Google confirmed the breach and have disabled the affected servers that were redirecting the malicious code. The ads themselves have been disabled as well.
